Cybersecurity firm Koi Security recently uncovered the sophisticated operations of the GreedyBear attack group, who managed to steal over $1 million in crypto using a multi-faceted approach. The group utilized 150 weaponized Firefox extensions, nearly 500 malicious executables, and numerous phishing websites to carry out their coordinated campaign.
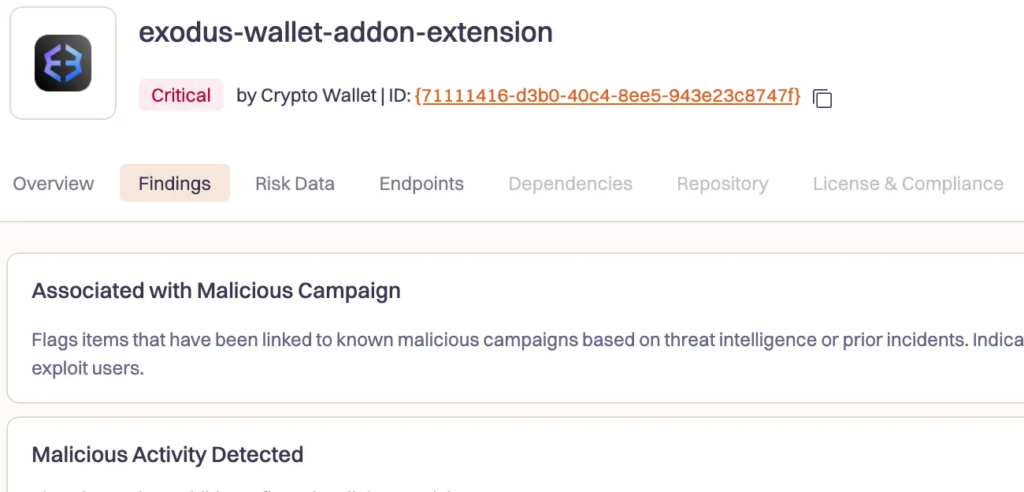
One of the key aspects of the attack was the use of a novel technique known as “Extension Hollowing.” This method involved creating seemingly legitimate extension portfolios on browser marketplaces before injecting them with malicious code. By building trust with users through innocuous extensions, the attackers were able to bypass marketplace security measures and successfully deploy their malicious payloads.
The GreedyBear group operated through a single server, allowing them to control their entire command infrastructure across different attack vectors. This centralized approach enabled them to coordinate activities across browser extensions, malware payloads, and scam websites. The group had evolved from a previous campaign called “Foxy Wallet” and demonstrated a high level of coordination and scale in their crypto-focused cybercrime operations.
The malicious Firefox extensions created by GreedyBear impersonated popular cryptocurrency wallets like MetaMask and TronLink, capturing user credentials directly from input fields. Additionally, the group utilized nearly 500 Windows executables targeting victims through Russian websites distributing cracked software. They also set up fake product landing pages advertising fraudulent hardware wallets and repair services.
Security researchers noted the presence of AI-generated code artifacts throughout the campaign, allowing the attackers to rapidly scale their operations and evade detection systems. The group’s expansion plans included confirmed Chrome extension variants, indicating a potential move to other browser ecosystems beyond Firefox.
The GreedyBear group’s Extension Hollowing technique involved posting fake positive reviews to build credibility before injecting malicious code into established extensions. This approach allowed them to maintain positive ratings and user trust while secretly stealing credentials. Victims reported significant losses as the extensions appeared to function normally while transmitting sensitive information to the attackers.
The group’s systematic manipulation of marketplace trust created sustainable channels for credential theft operations. This approach has raised concerns among industry players, with OKX and Microsoft issuing warnings earlier this year. The centralized server infrastructure used by GreedyBear facilitated streamlined operations across different attack vectors, enabling them to maintain operational security.
As crypto-focused cybercrime operations continue to evolve, traditional security solutions face increasing challenges. Recent large-scale incidents highlight the need for automated threat response mechanisms to protect assets from malicious actors. The current crypto security landscape has come under scrutiny for enabling unethical actions, particularly in recovery negotiations following security breaches.
In a recent interview with Cryptonews, Circuit CEO Harry Donnelly emphasized the importance of automated threat response to prevent assets from falling into the wrong hands. He criticized negotiation-based recovery methods and highlighted the need for better protection mechanisms to safeguard users’ assets.
The first half of 2025 has seen a significant increase in crypto-related losses, totaling $2.2 billion across 344 incidents. The prevalence of sophisticated cybercrime operations underscores the need for enhanced security measures to combat evolving threats in the crypto space.