A potential disaster in the npm supply chain was narrowly averted after attackers gained control of a verified developer’s credentials. Josh Junon, a well-respected developer with a significant GitHub contribution history, discovered that his npm account had been compromised. Users alerted him that his account was posting packages with backdoors to popular projects he was involved in. The attack was initiated through a deceptive email prompting a reset of his two-factor authentication.
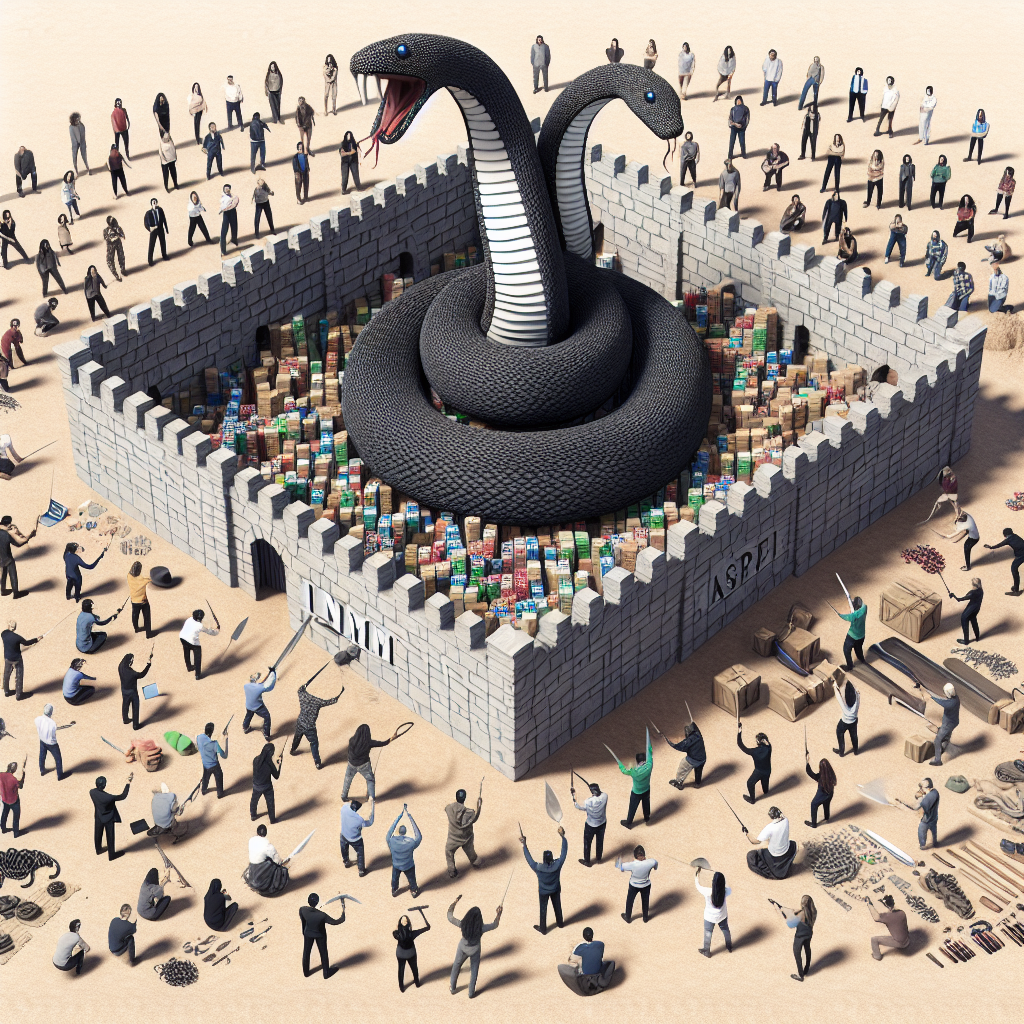
The compromised npm account, belonging to ‘qix,’ released malicious versions of numerous packages, including high-volume JavaScript projects like chalk, strip-ansi, color-convert, color-name, error-ex, simple-swizzle, and has-ansi. These packages were downloaded millions of times weekly. The malicious payload inserted in these packages was a crypto-clipper designed to steal funds by altering wallet addresses in network requests and intercepting crypto transactions.
The sophisticated malware utilized a crypto-stealer attack chain targeting cryptocurrency users through passive address-swapping and active transaction hijacking. By detecting wallet extensions like MetaMask, the malware swapped legitimate crypto addresses with attacker-controlled ones, making the swap nearly undetectable. In cases where wallets were present, outgoing transactions were intercepted and recipient addresses were modified before user confirmation, leading to funds being sent to the attacker.
Despite the severity of the attack, a crisis was averted within hours. NPM swiftly removed all compromised package versions, preventing further damage. Security experts commended the rapid response of the open-source community in containing the breach. While some labeled it as the “biggest supply chain attack in history,” others emphasized that the situation was swiftly contained with minimal financial loss.
To mitigate the threat posed by compromised packages, developers were advised to force-safe versions across their projects using package.json overrides. By specifying trusted versions of the affected packages and generating a fresh lockfile, developers could ensure the removal of any malicious dependencies. This proactive approach helped safeguard projects from potential vulnerabilities.
In conclusion, the npm supply chain attack serves as a reminder of the importance of maintaining robust security measures in the software development process. The collaborative efforts of the open-source community and swift response to security breaches demonstrate the resilience of the ecosystem. By staying vigilant and implementing best practices, developers can protect their projects from potential threats and contribute to a safer digital environment.